Article content
IT managers have a lot on their plates such as keeping systems operational, supporting business goals, troubleshooting endless issues, dealing with company policy, and administrative work—all while keeping up with a tight budget.
It’s easy to see why IT Asset Management (ITAM) or enterprise asset management can fall down the priority list. But neglecting ITAM or failing to leverage the right IT asset management software is like leaving money on the table.
A well-managed IT asset environment, supported by software asset management aplications, is not just about saving money, it's about keeping control, avoiding chaos, and ensuring future growth. Properly managed asset tracking ensures that.
Let’s explore why ITAM should be front and center in your IT strategy, and how tools like ALVAO Microsoft Asset Management software can make the process easier.
What Does IT Asset Management (ITAM) Stand For?
As IT manager, you probably have encounter ITAM or even the configuration management database (CMDB), but let’s make a quick refresh.
ITAM can be seen as a part of IT Service Management (ITSM).
But it's one of the ITIL4 practices of tracking, managing, and optimizing IT assets, both hardware such as laptops, phones, servers, printers and software assets such as subscriptions and licenses.
IT Asset Management is about understanding what you have, where it is, who is responsible for it, how it’s used, and how much it’s costing you.
At first, it sounds simple. But for many companies, it’s the unmanaged area, especially for enterprise asset management, that can lead to serious pain and high costs.
The Sore Pain Points of Ignoring IT Asset Management (ITAM)
Let’s outline the following scenario that are typical for many IT departments, especially those without proper IT asset inventory management:
You have over hundred or even thousands of devices scattered across multiple locations, software licenses that need renewal, and a budget that somehow never quite stretches far enough.
Managing all of this without best practices in IT asset management or using a dedicated ITAM asset management strategy can lead to too often to the following issues:
- Wasted Money – When IT teams don’t have visibility into their asset inventory, hardware or software inventory management, they often over-purchase assets or under-utilized them. Software licenses, particularly Microsoft licenses, can break the bank, as can unnecessary hardware purchases that balloon your expenses.
- Security Risks – Outdated, forgotten, or unpatched assets become a great deal for cyber threats. If you aren’t using cyber security asset management tools or tracking where assets are located and ensuring they’re up to date, you're creating security vulnerabilities.
- Compliance Nightmares – Fail to pass software audits because you’re not in compliance with licensing agreements can lead to significant fines and legal repercussions. It’s easier than you think to fall into non-compliance when there’s no clear record of who’s using what.
- Operational Inefficiency – Without IT inventory management software, IT support doesn’t have a clear overview of assets, troubleshooting takes time, upgrades are delayed, and the overall efficiency of your operations are inefficient.
These pain points are enough to keep any IT manager up at night. The good news? Both ITAM practices and software can help you solve these issues.
Why IT Managers Hesitate to Implement IT Asset Management (ITAM)
Before introducing the benefits of asset lifecycle management and ITAM, it’s crucial to mention the struggles IT managers often face when they think of ITAM implementation into their organization:
- Lack of Understanding of the Importance/Impact – Many don’t grasp the full impact of skipping ITAM or using a CMDB. They might know their IT maturity is weak. Their IT infrastructure management is hard to manage yet they miss the bigger picture, like potential cyber threats to the entire organization. Another issue is that IT teams often struggle to get an approval across the company with sponsorship and projects.
- Don’t know where to start – IT managers often don’t know where to begin. How to implement IT asset management tool and establish configuration management database (CMDB). They need to track areas to boost resilience, improve IT maturity, reduce risks, and gain visibility over their assets. Understanding where your assets are should be the first step.
- Too Busy with Current Tasks – Even if IT managers get the importance and know where to start, they’re swamped with incidents, requests, and maintaining IT infrastructure management. Managing various projects leaves no time for proper asset management and tracking.
- Lack of Skilled Talent – Not having the right people with the right skills to manage, IT asset management lifecycle can be a significant obstacle. The right team, along with asset management software, can make all the difference.
- Discouraged by Past Failures – Some have tried ITAM before and failed. This makes them hesitant to invest time and resources again, thinking it’s better spent elsewhere.
The Benefits and Practical Examples of IT Asset Management (ITAM)
Now that you see the massive potential of IT Asset Management, let’s talk about ITAM benefits and how to actually get there.
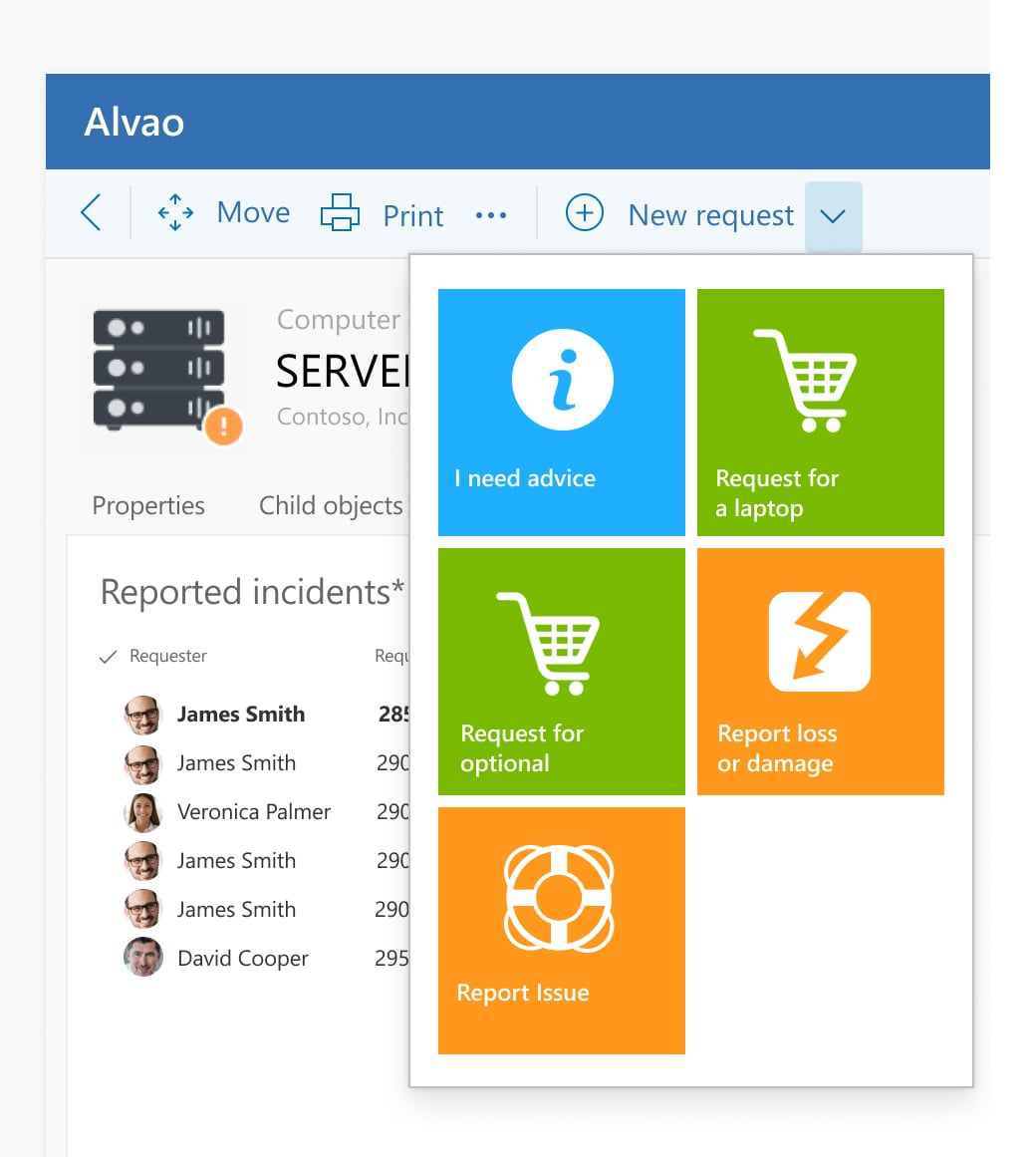
ITAM, when done manually, can be overwhelming. But with the right tools, like ALVAO Asset Management, you can automate much of the process and unlock its full potential.
1. Cost Savings Through Optimization
ITAM helps you uncover those “hidden costs”. By knowing exactly what hardware and software you have, you can avoid unnecessary purchases, renegotiate vendor contracts, and ensure licenses are properly allocated.
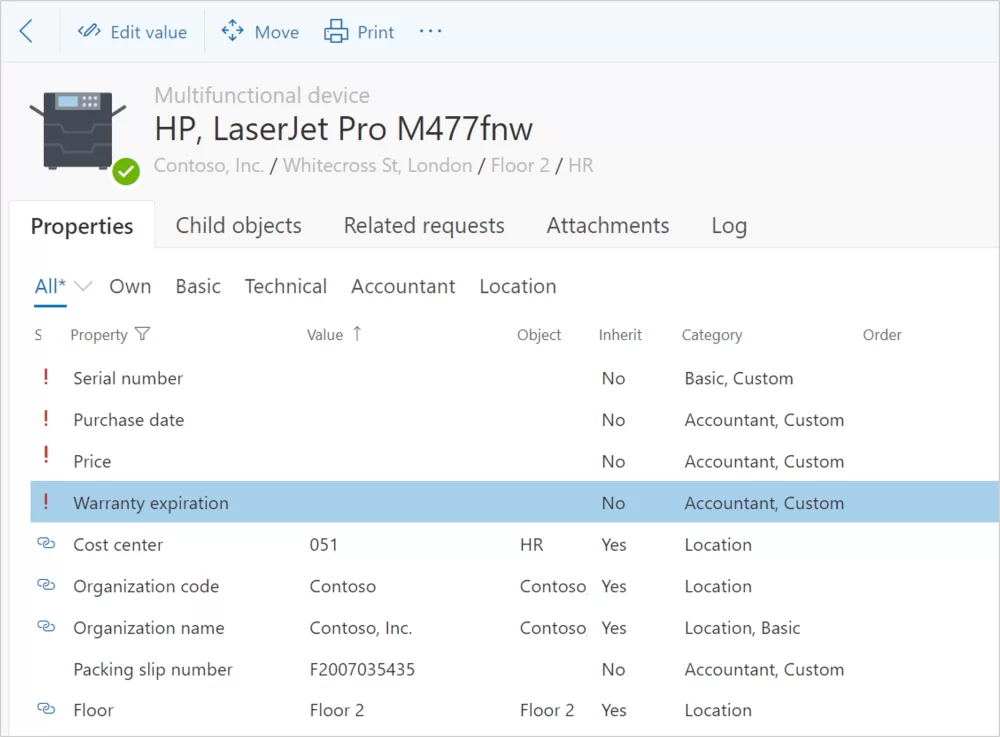
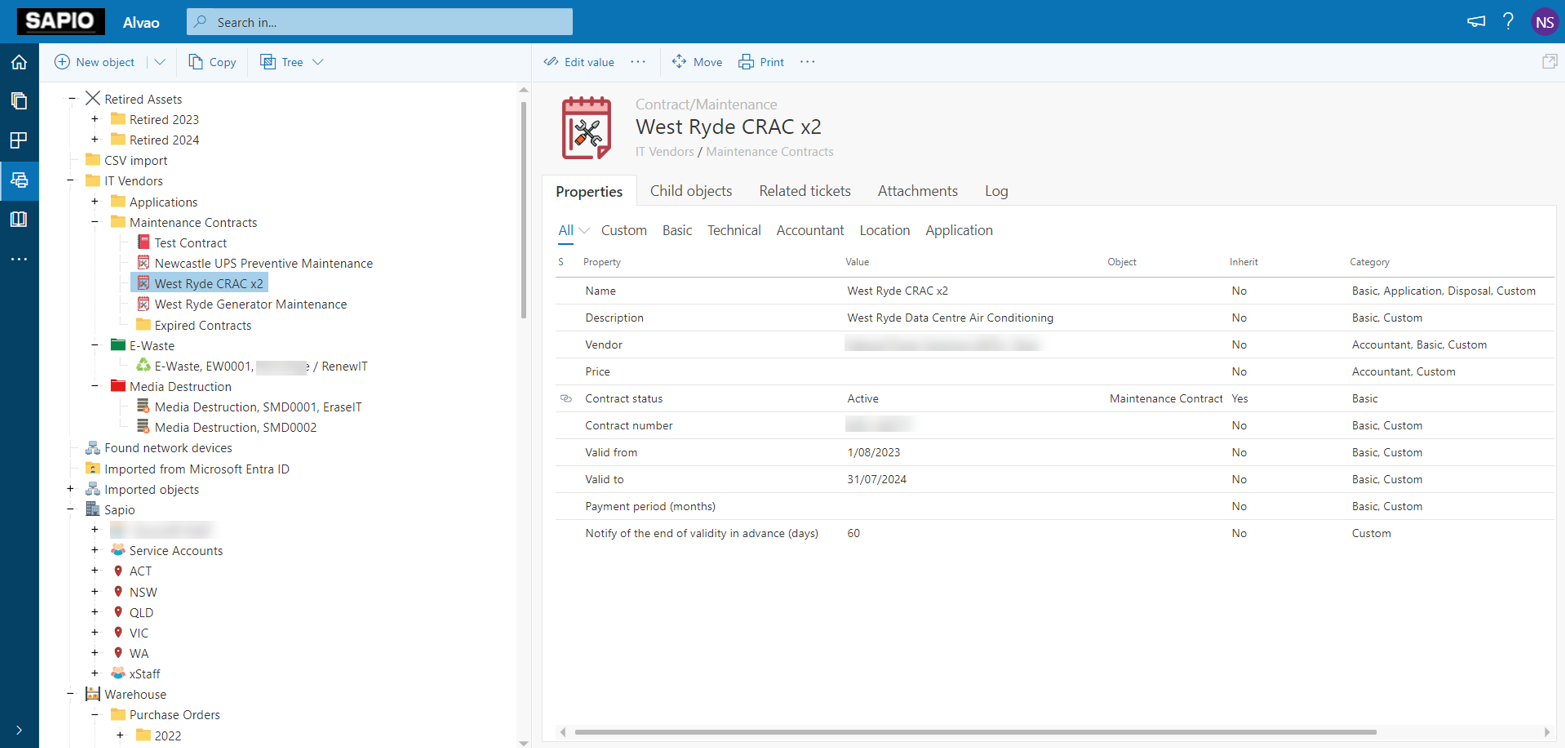
With ALVAO, all your IT assets, hardware or software, are visible in a single, intuitive platform. You can drill down to specific devices, see their status, and identify whether they’re approaching end-of-life.
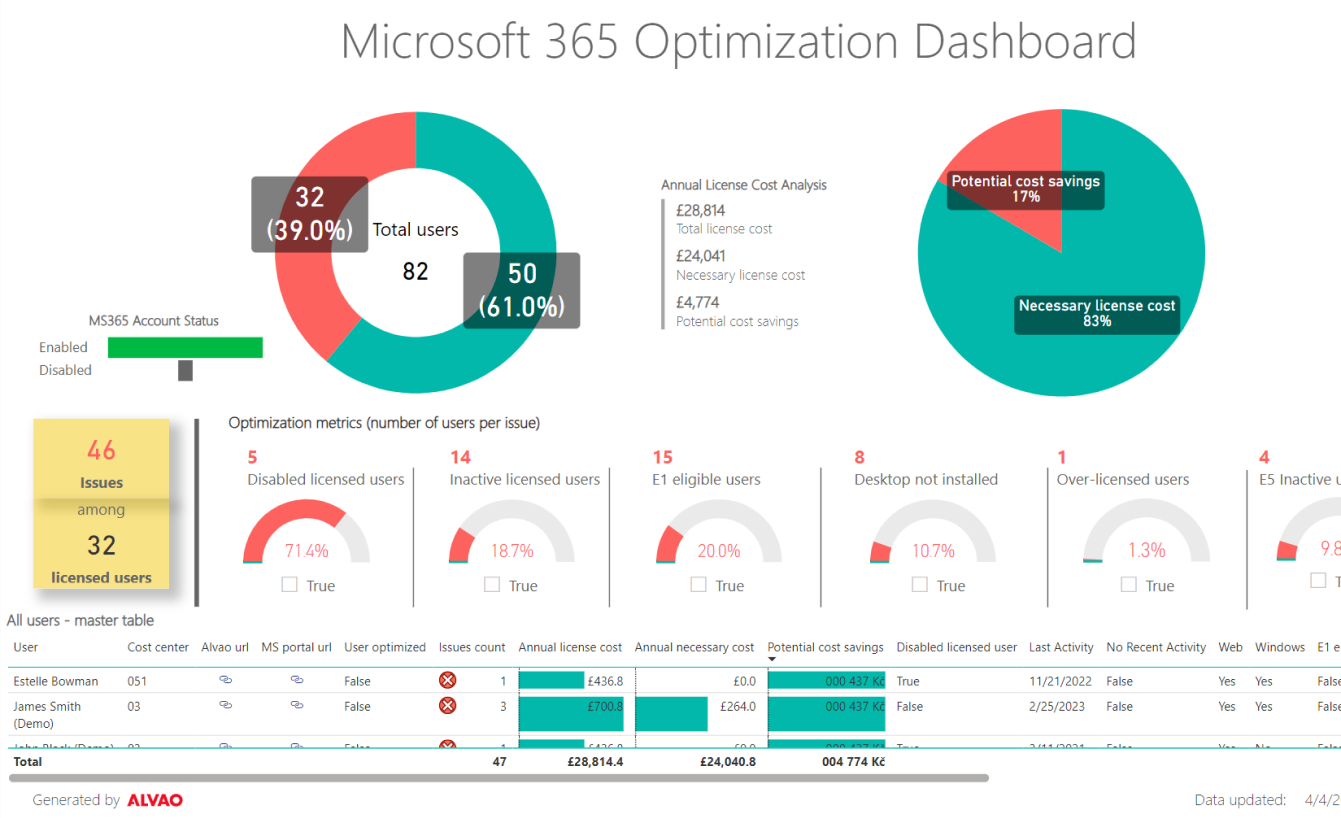
Example: An organization might have 500 Microsoft licenses, but only 300 active users. That’s 200 licenses wasted. By using ITAM to monitor and analyze software usage, you can cut those costs almost immediately.
2. Improved Security and Compliance
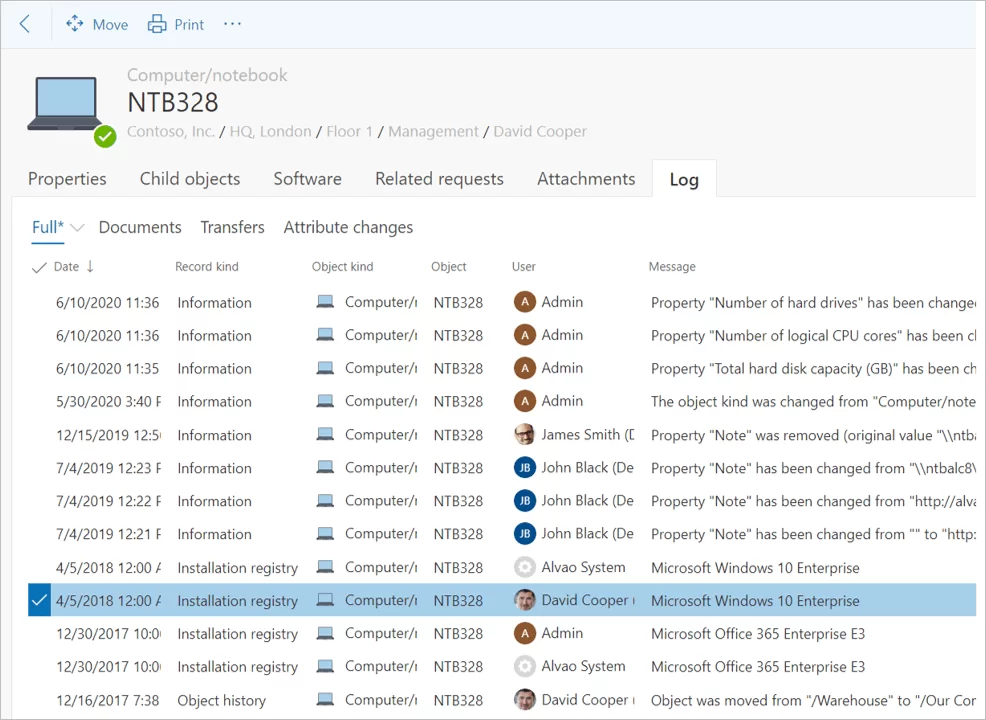
ITAM tracks every asset’s lifecycle, from procurement to retirement. Knowing which devices or software are approaching end-of-life ensures you patch vulnerabilities before they can be exploited.
Plus, you’ll always have a clear view of licensing compliance, significantly reducing your risk of audit penalties.
ALVAO is a software licensing solution that makes it easy to stay compliant with licensing and regulatory requirements by tracking software usage and expiration dates. Furthermore, ALVAO support to achieve ISO 27 001 certification. You’ll always be audit-ready. Learn how ALVAO helped Sapio to achieve ISO 27001 certification
Example: If a cybersecurity audit is coming up, ALVAO ITAM system will give you a complete map of every piece of software, ensuring you’re compliant with data security standards like ISO 27 001, SOC 2 Type 2 or NIS2.
3. Enhanced Operational Efficiency
Imagine an IT department where every support ticket is instantly tied to an accurate, up-to-date record of the user’s hardware and software. With ITAM, help desk teams can access that information in real time, leading to faster problem resolution and reduced downtime.
IT ticketing system and Asset Management can link incidents, changes and requests to the affected asset instantly showing you the complete history of the asset, including repairs and installed licenses.
4. Improved trust between IT and the business
ITAM doesn’t just help in day-to-day operations; it aids with long-term strategic decision-making. You can analyze data on asset performance and lifecycle trends to plan future purchases, predict costs, and ensure you’re investing in the right technology at the right time.
By doing so, IT builds trust with the business by demonstrating the real business value of ITAM, ultimately showcasing the value the IT department delivers.
Need to justify the ROI of your IT purchases? ALVAO’s reporting tools give you deep insights into asset utilization, helping you make informed decisions and show clear value to upper management.
5. Full Asset Visibility and Auditability
ITAM provides complete visibility and auditability of all assets. This transparency reduces Mean Time To Repair (MTTR), and minimizes value leakage, ultimately boosting operational resilience.
From procurement to disposal, ALVAO helps you manage each asset's lifecycle stage. You’ll know exactly when to replace aging hardware, ensuring no unexpected downtimes or security vulnerabilities.
Wrapping It Up: ITAM as a Strategic Investment
IT Asset Management or asset lifecycle management isn’t just an IT best practice—it’s a strategic investment that can help with cost savings, improve security, and streamline operations.
For too long, ITAM has been relegated to the "nice-to-have" category, but in today’s digital world, that’s no longer an option.
With the right asset inventory tools, like ALVAO Asset Management, implementing ITAM doesn’t have to be a hard battle. It’s time to prioritize IT asset management, take control of your assets, and set your IT department up for long-term success. Don’t let unmanaged assets hold your business back.
Are you ready to regain control? Start with ITAM today, and watch the benefits unfold.